Increase In Phishing SVG Attachments
There is an increase in SVG attachments used in phishing emails (Scalable Vector Graphics, an XML-based vector image format).
I took a look at the some samples mentioned in the Bleeping Computer article, and searched more samples on VirusTotal.
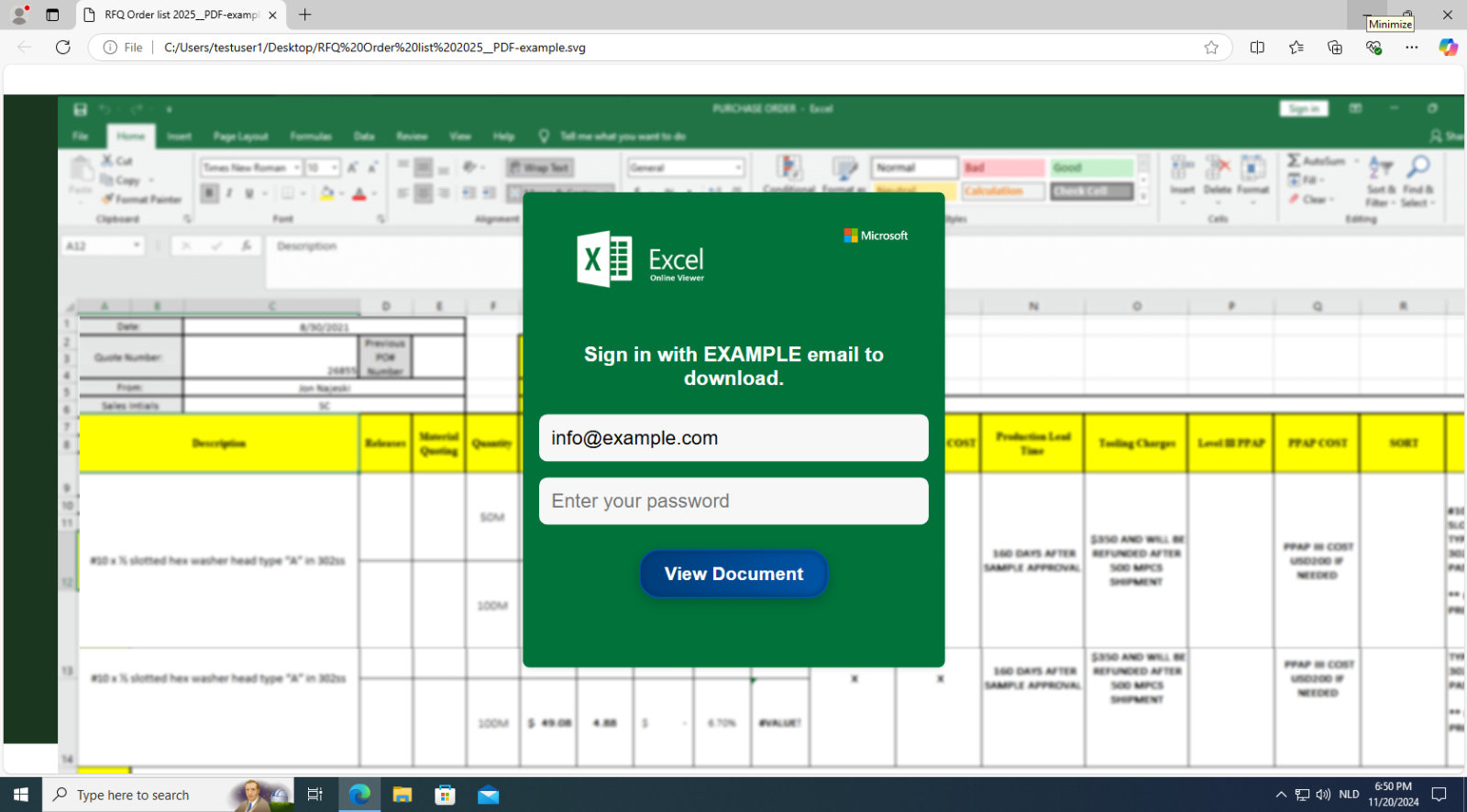
These samples contain HTML & JavaScript code to display a blurry Excel PNG image, and a phishing form asking for credentials. Like this one:
It contains 3 PNG files as data URIs, which can easily be extracted with base64dump.py:

You have the blurry Excel PNG:
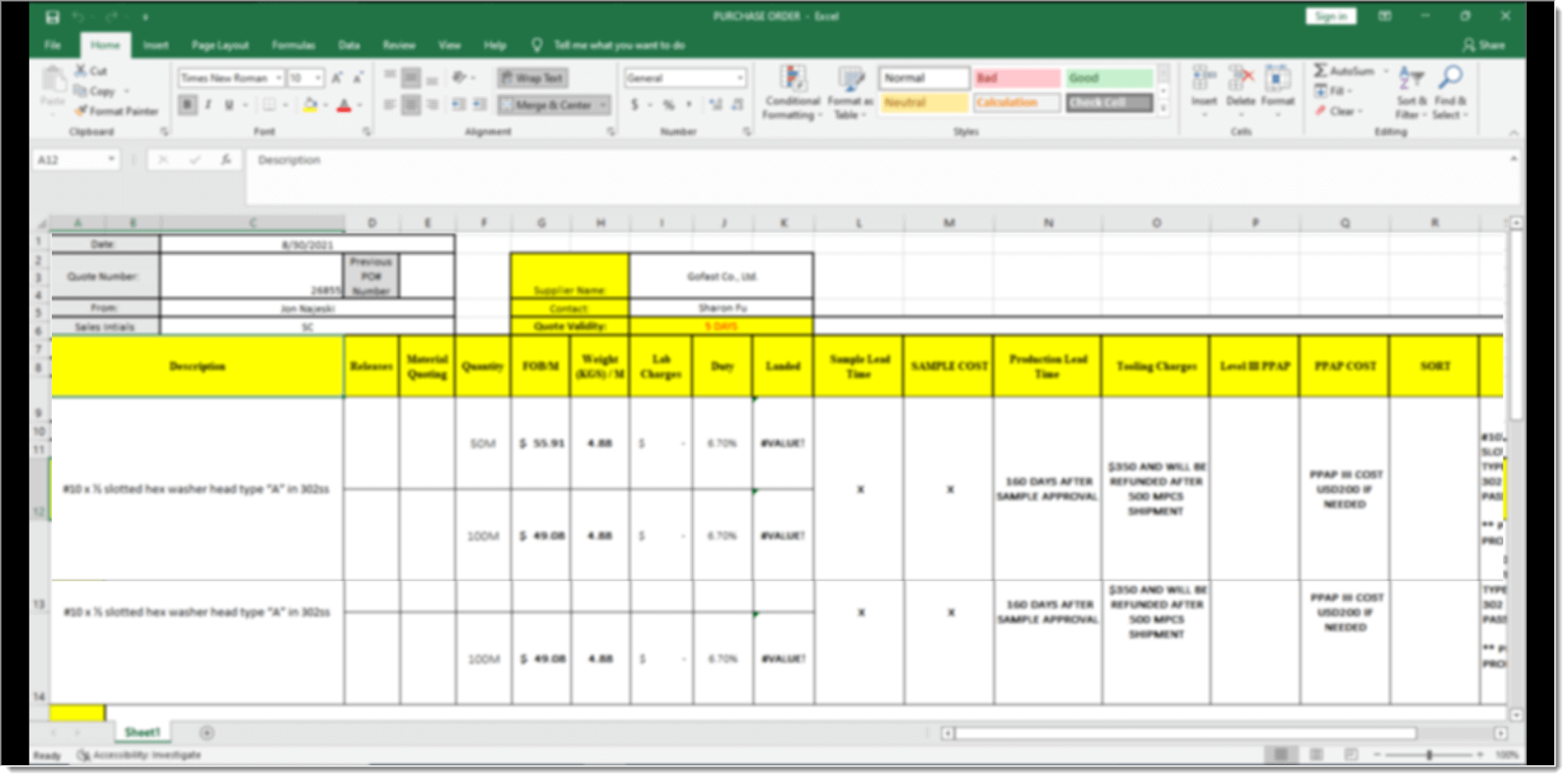
An Excel logo:

And a Microsoft logo:

I made some small changes to the sample, so that it would display an example.com email address, instead of a real victim's address that I would have to redact. The email address is hardcoded in BASE64 in the SVG file.
Here I made another example, using a SANS email address:
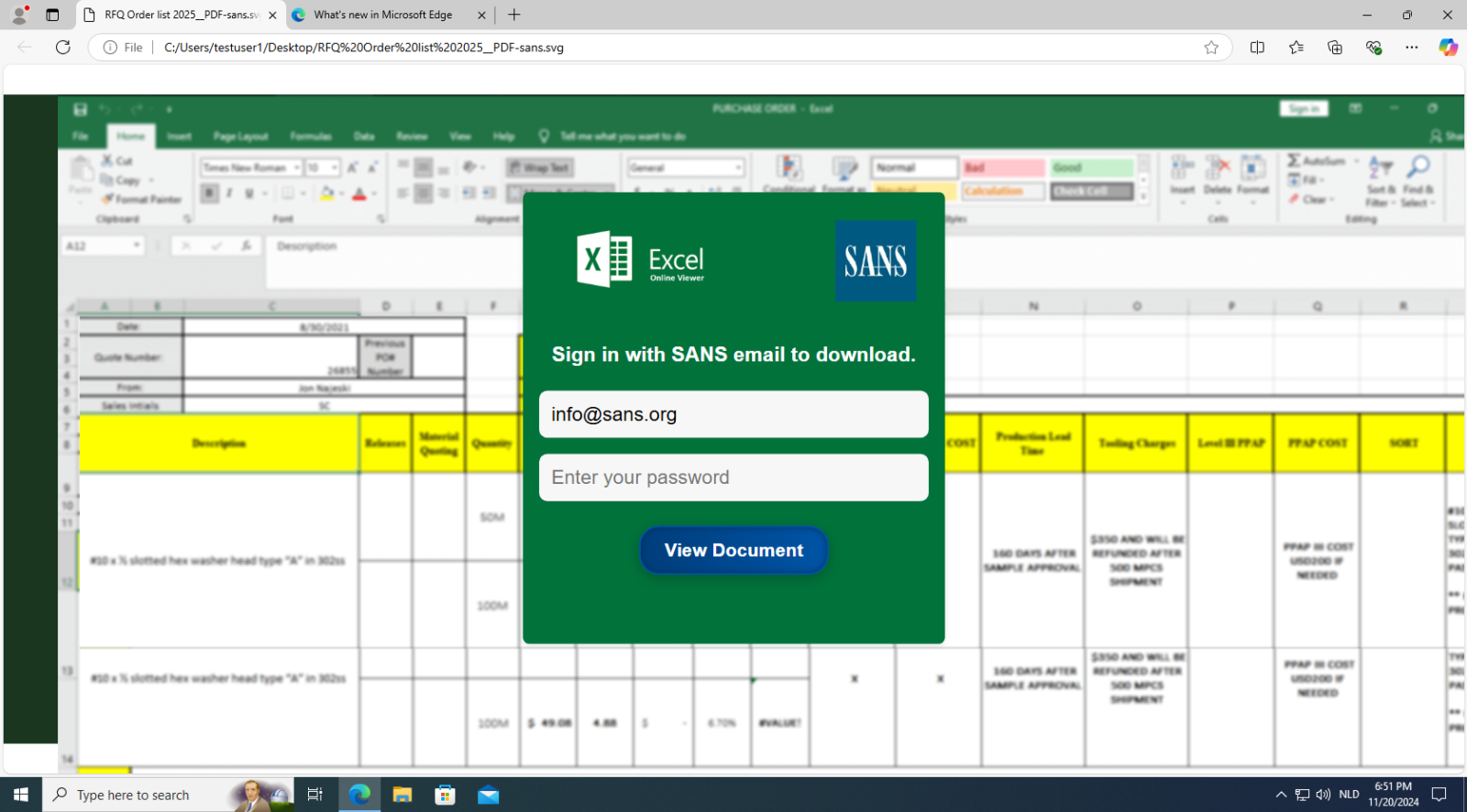
Do you see a difference, besides the SANS email address?
The SANS logo appears in the form!
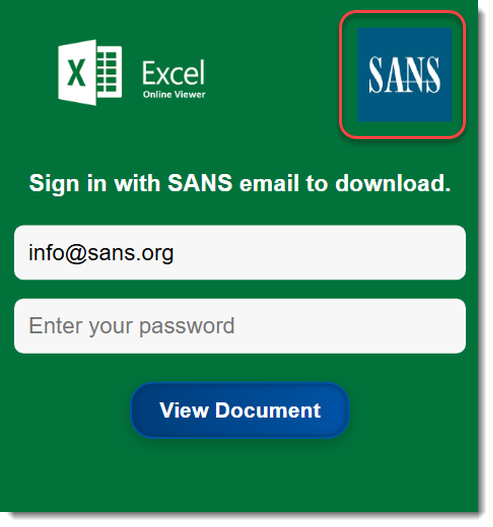
Where did that logo come from, it's not embedded in the SVG file!
That logo is retrieved using a web service: logo[.]clearbit[.com].
As an example, here is the retrieval of the Wikipedia logo:
Here are the URLs in this SVG file:

There's JavaScript code inside this SVG file to make a web request and display the appropriate logo (or the embedded Microsoft logo, if the service doesn't provide a logo).
And the last URL you see in this screenshot, is where the form data will be posted (the phished credentials).
That one is the most prevalent in the samples I got from VirusTotal, but there are some other ones:

And I have one sample with heavily obfuscated JavaScript, without cleartext URLs. I'll keep that one for another diary entry ...
Didier Stevens
Senior handler
blog.DidierStevens.com


Comments