Less is, umm, less?
Following vulnerabilities discovered in tools many Linux and Information Security enthusiasts use such as the 'strings' command and the bash shell, a new series of issues have been discovered in the 'less' command. Less is used to paginate output, and can be used to view the text contents of a file one page at a time. It can also receive data from a pipe. Examples: 'less myfile.txt' and 'xxd mybinfile | less'. One of the most attractive features of less is that you can move forwards and backwards through the output. It would not be unusual to use less to view files downloaded from the Internet for example. The problem is that less on some versions of Linux run a lesspipe script that invokes other utilities to actually view the contents of the files. Many of these should not be used to view files from an untrusted source. So local arbitrary code execution is possible if less is run on a malformed file. Back to using more?
References:
http://seclists.org/fulldisclosure/2014/Nov/74
http://linuxcommand.org/man_pages/less1.html
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
Security update for Adobe Flash player
Adobe has released an out of band security update for the Adobe Flash player. This is an additional update for CVE-2014-8439. Everyone either update or double check that Flash either is not installed or cannot be invoked via Internet web sites.
http://helpx.adobe.com/security/products/flash-player/apsb14-26.html
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
Guest diary: Detecting Suspicious Devices On-The-Fly
If you apply classic hardening rules (keep the patch level, use an AV, enable the firewall and use them with due diligence), modern operating systems are more and more difficult to compromise today. Extra tools like EMET could also raise the bar. On the other side, networks are more and more populated with unknown/personal devices or devices which provide multiple facilities like storage (NAS), printers (MFP), VoIP, IP camera, ...
Being easily compromised, they became a very good target to pivot into the network. They run out-of-the-box, just plug the network/power cables and they are ready to go! A classic vulnerability management process will detect such devices but you still have the risk to miss them if you run a monthly scan! To catch new devices on the fly and to have an immediate idea of their attack surface (example: is there a backdoor present), I'm using the following toolbox: Arpwatch, Nmap and OSSEC as the conductor.
Arpwatch is a tool for monitoring ARP traffic on a LAN. It can detect new MAC addresses or pairing changes (IP/MAC). Nmap is the most known port scanner and OSSEC is a log management tool with many features like a built-in HIDS.
A first good news is that Arpwatch log entries are processed by default in OSSEC. It has a great feature called "Active-Response" which allows to trigger actions (read: execute scripts) in specific conditions. In our case, I just created an active-response configuration to trigger a Nmap scan of any new device reported by Arpwatch:
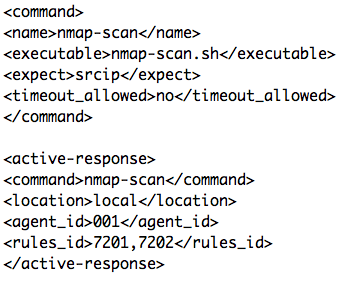
The above configuration specifies that nmap-scan.sh will be executed with the argument 'srcip' (reported by Arpwatch) on the agent '001' when the rule 7201 or 7202 will match (when a new host or a MAC address change is detected). The nmap-scan.sh script is based on the existing active-response scripts and spawns a Nmap scan:
nmap -sC -O -oG - -oN ${PWD}/../logs/${IP}.log ${IP} | grep Ports: >>${PWD}/../logs/gnmap.log
This command will output interesting information in grepable format to the gnmap.log file: the open ports (if any) of the detected IP like in the example below. One line per host will be generated:
Host: 192.168.254.65 (foo.bar.be) Ports: 22/open/tcp//ssh///, 80/open/tcp///,3306/open/tcp/// ...
OSSEC is a wonderful tool and can decode this by default. Just configure the gnmap.log as a new events source:
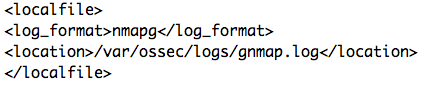
And new alerts will be generated:
2014 Oct 27 17:54:23 (shiva) 192.168.254.1->/var/ossec/logs/gnmap.log
Rule: 581 (level 8) -> 'Host information added.'
Host: 192.168.254.65 (foo.bar.be), open ports: 22(tcp) 80(tcp) 3306(tcp)
By using this technique, you will immediately detect new hosts connected to the network (or if an IP address is paired with a new MAC address) and you'll get the list of the services running on it as well as the detected operating system (if the fingerprinting is successful). Happy hunting!
Xavier Mertens

Comments